Damaging Information: LinkDaddy Cloud Services Press Release Introduces New Quality
Wiki Article
Secure and Efficient: Optimizing Cloud Solutions Advantage
In the fast-evolving landscape of cloud solutions, the intersection of protection and effectiveness stands as a vital juncture for companies seeking to harness the complete capacity of cloud computing. By diligently crafting a structure that prioritizes information security through security and gain access to control, businesses can strengthen their digital properties against impending cyber dangers. The quest for optimum efficiency does not finish there. The balance in between securing information and guaranteeing structured operations needs a strategic technique that necessitates a much deeper exploration into the intricate layers of cloud service monitoring.Information File Encryption Best Practices
When applying cloud services, employing durable information encryption best methods is vital to guard sensitive info properly. Information encryption involves encoding information in such a way that only licensed celebrations can access it, making certain discretion and security. One of the essential ideal methods is to make use of solid security formulas, such as AES (Advanced Encryption Standard) with keys of adequate length to protect data both in transportation and at rest.Furthermore, implementing proper key management strategies is important to keep the protection of encrypted information. This consists of safely generating, storing, and turning file encryption keys to stop unauthorized accessibility. It is likewise crucial to encrypt information not only during storage space however likewise during transmission between users and the cloud solution supplier to stop interception by harmful stars.
Source Allotment Optimization
To maximize the advantages of cloud services, companies must concentrate on maximizing resource allowance for efficient operations and cost-effectiveness. Source appropriation optimization involves tactically distributing computer resources such as processing network, power, and storage space bandwidth to satisfy the varying needs of applications and work. By executing automated source allocation mechanisms, organizations can dynamically change source circulation based on real-time needs, making sure optimum efficiency without unneeded under or over-provisioning.Reliable resource allowance optimization leads to enhanced scalability, as resources can be scaled up or down based on use patterns, resulting in improved flexibility and responsiveness to transforming service demands. In conclusion, source allowance optimization is important for companies looking to take advantage of cloud services successfully and firmly.
Multi-factor Verification Application
Executing multi-factor verification improves the safety posture of companies by requiring added verification actions beyond simply a password. This included layer of safety and security significantly minimizes the risk of unapproved accessibility to sensitive data and systems. Multi-factor authentication normally combines something the individual recognizes (like a password) with something they have (such as a mobile device) or something they are (like a fingerprint) By including several variables, the probability of a cybercriminal bypassing the verification process is considerably diminished.Organizations can select from various techniques of multi-factor verification, consisting of text codes, biometric scans, hardware tokens, or verification applications. Each approach offers its very own level of protection and ease, permitting organizations to select the most suitable alternative based on their distinct needs and sources.
Furthermore, multi-factor authentication is crucial in safeguarding remote accessibility to cloud solutions. With the increasing pattern of remote job, ensuring that only licensed personnel can access vital systems and information is paramount. By executing multi-factor verification, companies can strengthen their defenses versus possible security breaches and data theft.

Calamity Recovery Planning Techniques
In today's digital landscape, efficient catastrophe recovery planning methods are crucial for organizations to mitigate the impact of unanticipated disruptions on their data and operations integrity. A robust disaster recovery plan entails identifying useful site potential dangers, examining their possible effect, and carrying out aggressive procedures to make sure service connection. One essential aspect of calamity recovery preparation is developing back-ups of vital data and systems, both on-site and in the cloud, to enable swift remediation in case of an incident.Moreover, organizations need to carry out normal testing and simulations of their catastrophe recovery procedures to identify any type of weak points and improve action times. Additionally, leveraging published here cloud services for catastrophe recuperation can offer cost-efficiency, versatility, and scalability contrasted to typical on-premises options.
Efficiency Keeping Track Of Tools
Efficiency surveillance tools play a critical role in supplying real-time understandings right into the health and efficiency of an organization's applications and systems. These devices enable companies to track different efficiency metrics, such as action times, source application, and throughput, enabling them to determine traffic jams or possible concerns proactively. By continually monitoring essential performance signs, organizations can guarantee ideal performance, click here to read determine trends, and make educated choices to improve their general operational effectiveness.One more extensively utilized tool is Zabbix, using monitoring capabilities for networks, web servers, virtual makers, and cloud services. Zabbix's straightforward interface and personalized attributes make it a useful asset for companies seeking durable efficiency tracking remedies.
Final Thought
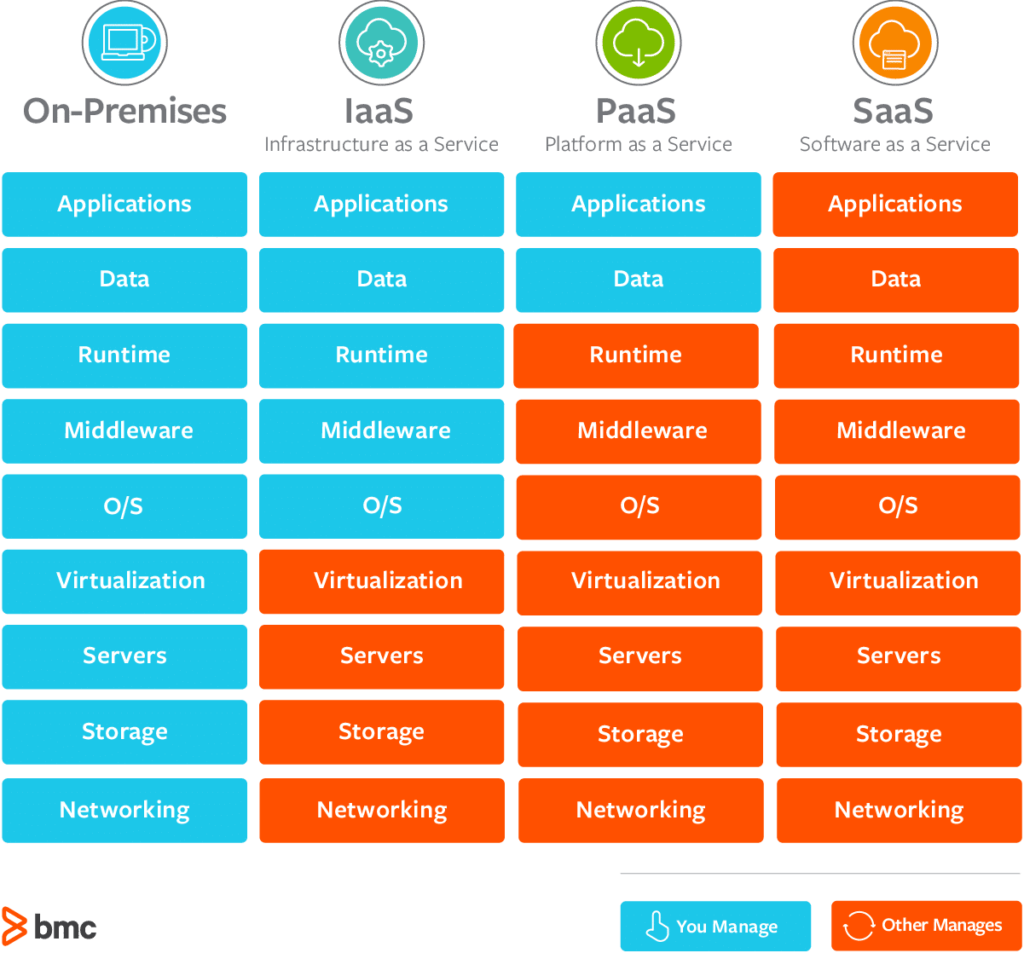
In the fast-evolving landscape of cloud services, the crossway of protection and efficiency stands as a critical juncture for organizations seeking to harness the full capacity of cloud computer. The balance between protecting data and making sure structured operations needs a calculated approach that necessitates a deeper exploration into the intricate layers of cloud solution monitoring.
When applying cloud solutions, employing robust data encryption best practices is critical to protect sensitive details properly.To make best use of the benefits of cloud solutions, organizations should focus on optimizing source allotment for efficient operations and cost-effectiveness - linkdaddy cloud services press release. In final thought, resource allocation optimization is crucial for companies looking to take advantage of cloud solutions efficiently and safely
Report this wiki page